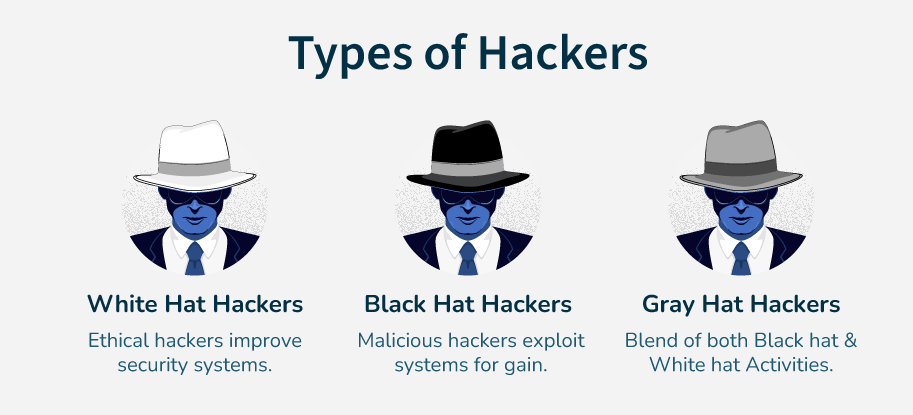
Hacking is often misunderstood. Movies and media portray hackers as cybercriminals, but the reality is much more nuanced. In the world of cybersecurity, hackers are categorized based on intent, legality, and methods. Understanding the different types of hackers is essential for anyone interested in ethical hacking or cybersecurity careers in 2026.
This guide explains white hat, black hat, and gray hat hackers, their roles, legal boundaries, and how aspiring ethical hackers should navigate these distinctions.
Table of Contents
What Is a Hacker?
A hacker is someone who identifies and exploits weaknesses in computer systems, networks, or applications. Hacking itself is a neutral skill, it can be used for good or malicious purposes.
Hacker types are defined primarily by intent and legal compliance.
White Hat Hackers – The Ethical Hackers
White hat hackers, also called ethical hackers, use their skills legally and responsibly to improve security. They help organizations protect systems from cybercriminals.
Key Responsibilities
- Performing penetration tests
- Conducting vulnerability assessments
- Recommending security improvements
- Educating staff on cybersecurity
Tools and Techniques
- Network scanning (Nmap)
- Exploitation frameworks (Metasploit)
- Web application testing (Burp Suite)
Legal Status
White hat hackers always operate with written permission and within a defined scope. Unauthorized access, even with good intentions, is illegal.
Career Opportunities
- Penetration tester
- Security consultant
- Red team specialist
- Bug bounty hunter
Bug bounty programslike HackerOne allow white hat hackers to earn legally by finding vulnerabilities
Black Hat Hackers – The Cybercriminals
Black hat hackers are individuals who exploit systems illegally for personal gain, notoriety, or disruption. They disregard laws and ethics.
Common Activities
- Stealing data or credentials
- Deploying ransomware or malware
- Defacing websites
- Conducting phishing attacks
Legal Status
Black hat activities are illegal worldwide. Offenders face criminal charges, fines, and imprisonment.
Impact
- Financial losses for organizations
- Data breaches affecting millions
- Loss of trust in digital systems
Gray Hat Hackers – The Ambiguous Hackers
Gray hat hackers operate between ethical and unethical boundaries. They may access systems without permission but without malicious intent. The legality of gray hat hacking depends on context and jurisdiction.
Examples of Gray Hat Behavior
- Discovering a vulnerability without authorization but reporting it publicly
- Testing a system to highlight weaknesses without prior permission
- Attempting to help organizations without formal engagement
Legal Status
Gray hat hacking can lead to legal consequences if it violates local laws, even if no harm was intended. Understanding the law is critical.
Ethical Considerations
- Always try to obtain permission
- Avoid causing disruption
- Document findings responsibly
Key Differences Between Hacker Types
| Feature | White Hat | Black Hat | Gray Hat |
|---|---|---|---|
| Intent | Ethical, protective | Malicious, personal gain | Mixed / ambiguous |
| Legality | Legal | Illegal | Often illegal without permission |
| Tools Used | Ethical hacking tools | Malware, exploits | Both legal and hacking tools |
| Career Opportunities | Security jobs, bug bounties | None (criminal activity) | Limited legal opportunities |
Why Understanding Hacker Types Matters
For aspiring ethical hackers:
- Knowing hacker types clarifies legal boundaries
- Helps in career planning
- Guides tool and methodology choices
- Prevents accidental legal violations
Organizations also categorize hackers to develop security defenses, such as:
- Red teams (simulate black hat attacks)
- Blue teams (defend against attacks)
- Purple teams (coordinate offense and defense)
How to Become a White Hat Hacker in 2026
Becoming a professional white hat hacker involves:
- Learning networking and operating systems
- Mastering ethical hacking tools
- Practicing legally on platforms
- Getting certified
- CEH (Certified Ethical Hacker)
- OSCP (Offensive Security Certified Professional)
Final Thoughts
Not all hackers are criminals. In 2026, ethical hackers (white hats) play a critical role in cybersecurity, while black hats pose threats and gray hats occupy a gray area of ethics and legality. Understanding these distinctions is the foundation of a successful career in cybersecurity. Always choose ethical practices and stay within legal boundaries to build credibility and long-term career growth.
Also Check Ethical Hacking Roadmap – From Beginner to Professional (2026 Guide)
1 thought on “Types of Hackers – White Hat vs Black Hat vs Gray Hat 2026”